
Limitless customization options & Elementor compatibility let anyone create a beautiful website with Valiance.

We know how to develop a website according to what you need. We think as a consumer, and we know our clients' users' requirements and needs of the market.
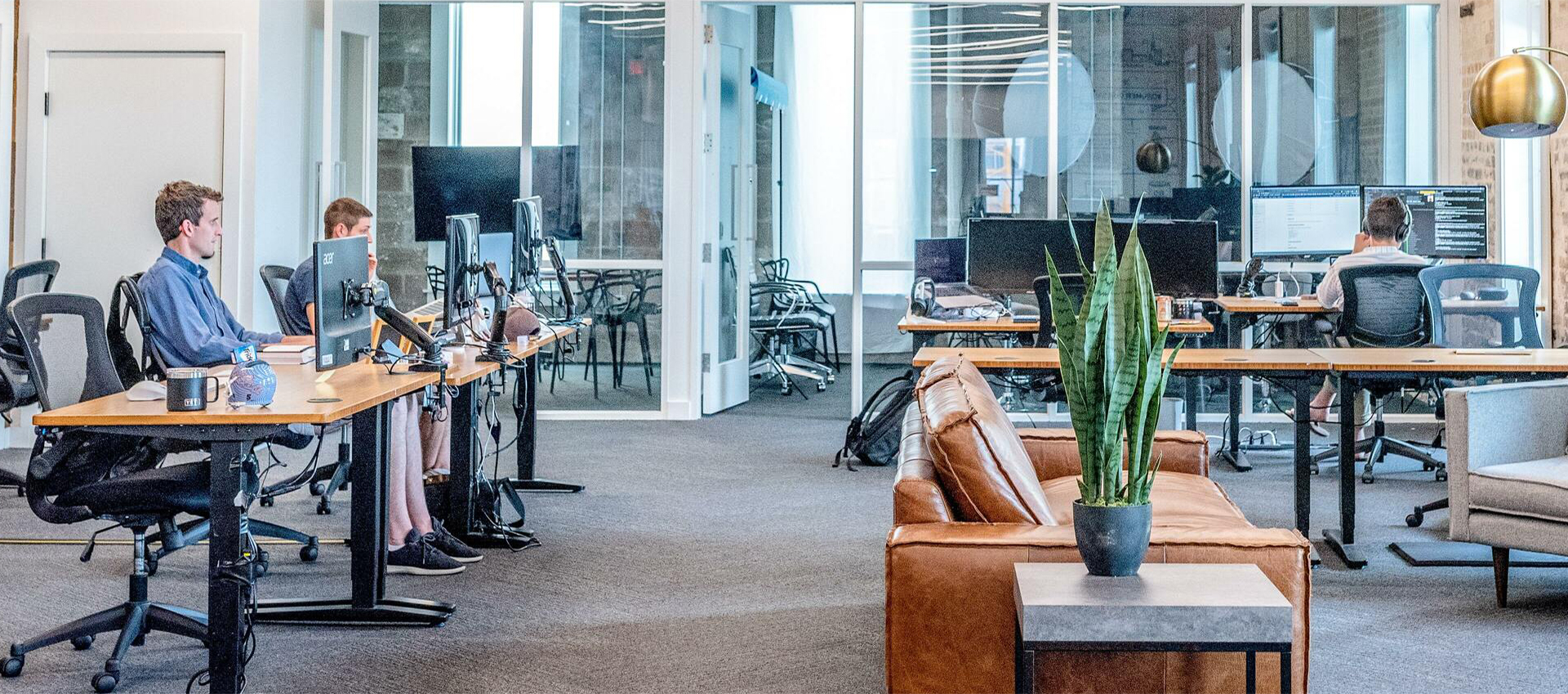
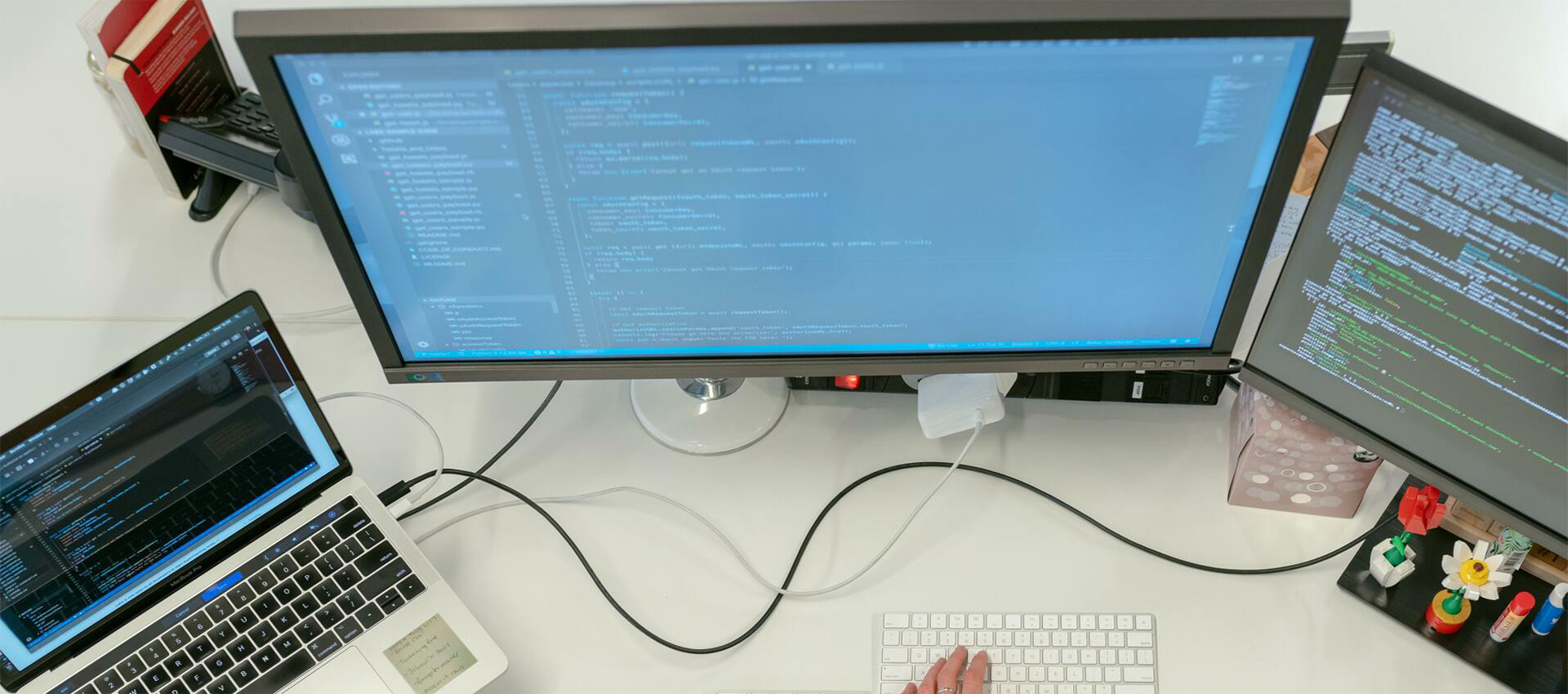
VIEW MOREOur team of developers works together to find the best solutions for our clients. in native or cross-platform development.
Cyber attacks are spam attempts to access or damage a computer system. We are experts in protecting your valuable data from cyber attacks.
VIEW MORESocial Media is a platform where your potential customers engage, and that's where you should be, it's time to get our Social Media marketing services.
VIEW MOREWe create search engine campaigns to make you stand out from your competition and get your target audience in just a few clicks.
If they don’t see you, you don’t exist. Especially on the Internet. show your service or product to billions of people on the internet with our SEO expert team.
VIEW MOREAs an expert agency in UX and UI Design, we take care of creating an optimal interaction between people and products or services and get the design according to your needs.
VIEW MOREWebsite is the image of your business that transmits to the rest of the world. Our designers will advise you on a modern and functional design.
Our Web development company did not limit your web design and development! We are experts in achieving results.

We Blue Horn web development company is UK base Full Stack Agency. Our main purpose is to connect your Business or Brand with the target audience.
Making it shine with technology. We are passionate about web and app development! We have an experienced team in Digital marketing.
A successful strategic partnership is mutually beneficial for both companies involved. Each must see a clear benefit from the deal. The responsibilities of our web development company in the implementation of the business strategy must be clearly identified.
Our Fixed Price model hire service is dedicated to providing the solution you need at 100% fixed price and with no hidden extra charges with ease of mind.
Let's TalkHire a Dedicated Team Model enables you to hire a dedicated team to take care of your product or service. It will be responsible for researching new markets.
Hire a TeamOnsite Development Model is preferred when the client needs to add temporary resources for on-site development. This type of agreement is cost-effective.
Get Resource





Blue Horn Web Development Company stands out among the best web development companies in the UK. Our professional team creating an Incredible Website is an improved method after years of creating web page. we ensure the highest quality in each project, achieving impressive results in % of sales compared to the typical website design and Template.
The design is probably one of the most relevant parts of a website since everything enters through the eyes. With a good design, you will have more confidence in the product and you will be able to sell it more expensive due to the fact that the sensation will be of higher quality and it will be easier for users to browse the web and stay longer, improving SEO and memory branded.
Investing in the web design of your company is transformed into profitability. Being able to count on an experienced web design agency that you can trust is essential to achieve your goals or improving the brand experience.
All the content and material necessary to develop a website: texts, logo, photographs, and other graphics, are provided by the client. It is important that it is you or someone on your team, who is responsible for collecting, writing, and structuring the information on your site so that the objectives of our web development company regarding the information you want to communicate are fulfilled in the letter.
Having a well-optimized web page with adequate web positioning helps to generate free traffic to it, and that helps save on advertising costs in search campaigns since paying Google Ads for an advertising campaign is sometimes expensive.

Subscribe to our weekly newsletter below and never miss the latest product or an exclusive offer.
